Despite headlines all month showing the scope of compromised personal information in attacks on Equifax, Yahoo and the SEC, many advisors still aren’t taking cybersecurity seriously.
An examination of more than 1,200 investment advisors by the North American Securities Administrators Association uncovered 698 deficiencies, including no or inadequate cybersecurity insurance, no testing of cybersecurity vulnerability, lack of procedures regarding securing or limiting access to devices, no technology specialist or consultant and a lack of procedures regarding hardware and software updates or upgrades.
Frank Quinlan, a counsel to the law firm Newmeyer & Dillion, who has a background in cybersecurity with the U.S. military, says that because of the amount and type of client information advisors hold, not to mention money and other assets, advisors have to understand that attacks are coming and they are targets, no matter how big or small their firms. Quinlan says advisors absolutely must spend some time understanding information security principles to protect themselves and clients.
He recommends advisors get the NASAA’s “Cybersecurity Checklist for Investment Advisors’ which Quinlan says is written to be easily understood by advisors and will especially help independent registered investment advisors and small firms get up-to-snuff. But for those worried about these headline-grabbing attacks and what they can do immediately to improve security, Quinlan recommends three key steps.
The first is to read through the National Institutes of Standards and Technology’s guide on the fundamentals of small business information security to have a baseline understanding of the terms and concepts. “[It is] your operational manual for securing a small business,” Quinlan said.
Second step, advisors need to assess their own enterprises, identify the risks and how the firms are managing them. For advisors feeling overwhelmed by technology, Quinlan recommends bringing in an outside expert or consultant who can go through it with them.
The third step is what he calls a “Death Star analysis” to pinpoint what risks could actually destroy the business (like the small thermal exhaust port Luke Skywalker used to destroy the Death Star in the 1977’s Star Wars). From there, advisors can insure against it.
“You’re insuring against human error; human error is ultimately what takes everyone down,” Quinlan said. “It’s not possible to protect against everything. It just isn’t.”
Even though it’s an added expense, Quinlan says advisors should consider Equifax—a company that knew about its vulnerabilities but made a business decision not to protect against them.
External IT Vice President of solutions and security Justin Kapahi added that this negligence might result in Equifax facing criminal charges and why advisors could also be liable to prosecution if they face a similar data breach. Kapahi added that advisors need to prove to clients and regulators alike that they are making security one of their highest priorities.
The problem he sees is too many firms are still brushing the risk off because they think they’re too small to be a target. But everyone needs to take care of the basics: making sure all systems have the latest updates, evaluate the firm’s security, have proper controls in place and use a firewall.
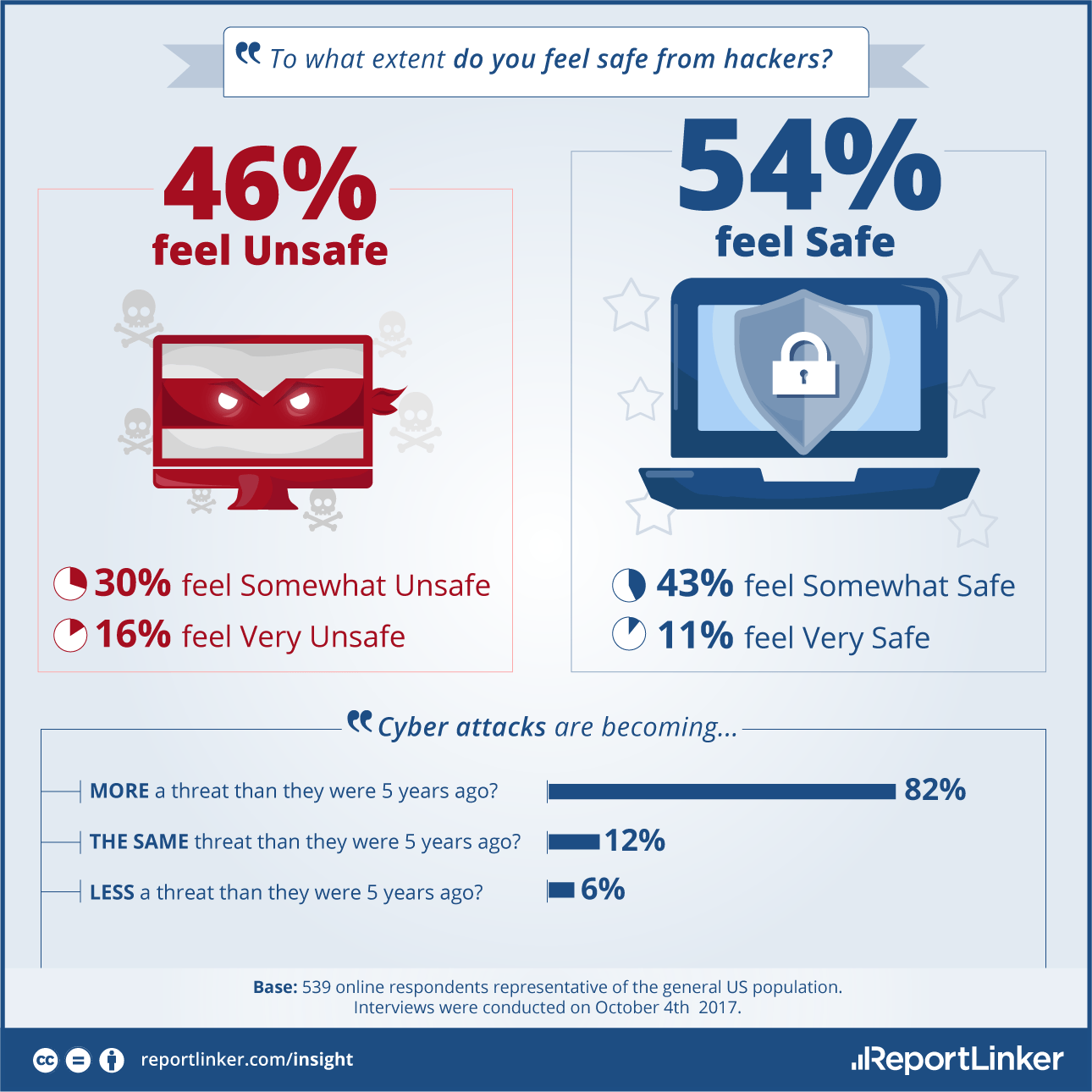
Beyond that, Kapahi says the next level is educating employees and clients alike on staying safe online. A study published earlier in October found that the two most popular passwords are still “123456” and “password.” The same study found that while the vast majority of Americans agree data breaches are more of a threat now than they were five years ago, most don’t feel they are personally at risk.
“Get humans to be the first line of defense,” Kapahi said. “Don’t open attachments, don’t transfer money online and don’t send credit card information over email.”
Kapahi added that advisors should make cybersecurity a higher priority when it comes to the due diligence process for technology vendors. Advisors need to ask to see documentation around a vendor’s security process and ask questions to ensure that the vendor meets the same standards as the advisor’s own firm. If the firm’s decision-makers don’t know which questions to ask, they need to bring on someone who does.
Phil Tully, a principle data scientist at ZeroFox, which works with enterprise companies to combat social media threats, says targeted attacks using social media is a growing area of concern for financial services professionals. Hackers are targeting clients with specific hashtags connected to brands they follow and redirecting them to pages asking for login credentials. Other times, they are looking for advisors’ LinkedIn contracts and delivering specific attacks using fake domains, a mock-up of the firm’s website and logo, and persuasive messaging.
Tully says the answer isn’t to just disengage from social media—Warren Buffet, for example, has Twitter but isn’t active, and many people have created fake accounts to impersonate him—but to be mindful of the information put out there.
“Be very careful about how you disclose personal information online,” Tully said. “Act like everything you’re going to type into the Internet will be released some day.”

