In case you are not a deeply committed sci-fi fan, Cybermen were a creation of the 1960s British television series, Dr. Who. Over time, these once-organic creatures replaced their body parts with artificial ones, mainly in order to optimize their self-preservation. With a bit of imagination, we could make the argument that today’s lifestyle is becoming eerily similar. Maybe not so much in the body-parts department, but the automation of core functions has become commonplace. Modern society is now dominated by networks that are not only social, but cyber, in nature—including information technology, computers, and virtual reality.
Recent events are a testament to the growing complexity and challenges of an ever-expanding cyber world. Domestically, we have experienced multiple corporate data breaches, including one against prominent U.S. retailer Target. Assuming that the hack on the Sony Corporation was not just a clever publicity stunt to promote their movie “The Interview,” the topic is becoming an item of international affairs and potentially even geopolitical conflict; nothing short of proof to this assumption is a map, updated daily, accounting for known digital attacks—pretty much right out of an action movie.
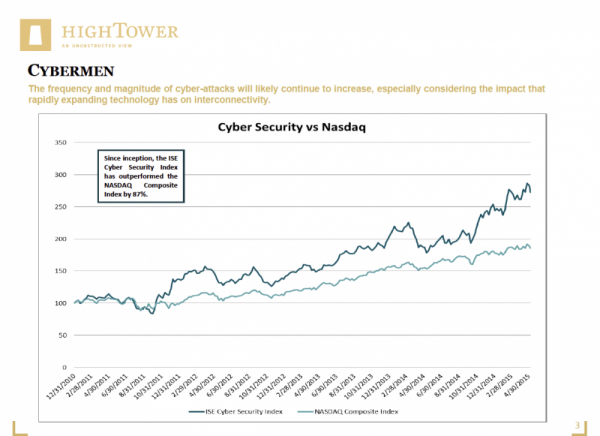
Not surprisingly, the frequency and magnitude of cyberattacks will likely continue to increase, especially considering the impact that rapidly expanding technology has on interconnectivity. Gartner, Inc. forecasts that 4.9 billion “connected things,” otherwise known as the “Internet of Things (IoT),” will be in use in 2015 (up 30 percent from 2014) and will reach 25 billion by 2020. According to a report from PwC surveying more than 9,700 security, IT, and business executives, cyber hacks are increasing at a significant rate: an estimated 66 percent compound annual growth rate since 2009, with 3.4 million incidents detected in 2009 having exploded to a staggering 42.8 million in 2014.
The impact of cybercrime on the global economy amounts to a total of $445 billion per year (2013 figures), but, unfortunately, this number is also getting bigger. The data breach at Target not only impacted private data of 40 million shoppers, but is estimated to have cost the company nearly $150 million (amounting to 3 percent of annual profits in both 2013 and 2014). On the other side of the spectrum is the necessary investment companies must make to “ramp-up” security measures. After data of 76 million clients was compromised at investment bank J.P. Morgan (JPM), the company announced planned spending of $250 million annually to secure its cyber world. Further, 13 other financial institutions were targeted by the same hackers during the JPM “coup.”
Where there is a strong trend paired with significant spending, there is typically an opportunity for investors to capture. No, we are not suggesting “shorting” potential targets (companies) of cyberattacks, but rather focusing on a better selection process (including determining over- and/or underweights as part of an asset allocation). For example, car and aircraft manufacturers will have to address the risk and related cost of remote access to their equipment—a threat that has become more prominent in recent months. A constructive investment focus on the “long side” of this trade, then, should consider companies catering to new and necessary security measures (also applicable to the above banking and retail breaches). In this respect, a slew of ETFs and mutual funds are emerging; for now, these are a means to help identify and take advantage of cybersecurity-related opportunities—but perhaps someday we will be investing in funds specifically focused on companies developing bionic body parts…or even Cybermen.
Matthias Paul Kuhlmey is a Partner and Head of Global Investment Solutions (GIS) at HighTower Advisors. He serves as wealth manager to High Net Worth and Ultra-High Net Worth Individuals, Family Offices, and Institutions.